List of Linux Distros for Hacking
These distributions are mainly used for pen-testing & to reveal & fix the vulnerabilities. Here is list of Linux Distros for Information Security & Hacking
Hey Friends! Today I am here with a collection and some info on the Linux Distros used for Hacking, Security, Rescue etc.
These distros are mainly used for pen-testing to reveal, recover, or heal vulnerabilities.
In my previous post on Linux Distros, I listed some valuable Distros according to their usefulness. Here is the list of Some most commonly used Hacking/Security Distros. You can test the below-listed distros on Virtual Box or VMWare.
You can see how to install Linux on Virtual Box or VMWare here:

Here is the list of Linux Distros for Hacking:
Parrot Security

Parrot Security OS is Debian based Linux Distribution designed for PenTesting, Vulnerability Assessment and Mitigation, Computer Forensics and other Cyber Security related tasks. It also has different distros dedicated to the required usage, which can be seen at https://parrotlinux.org/download-security.php.
Parrot also offers a Home Edition for daily use, a lightweight and encryption-enabled platform to gain security and anonymised web access.
Kali Linux

From the creators of BackTrack comes Kali Linux, the most advanced and versatile penetration testing distribution ever created. BackTrack has grown far beyond its humble roots as a live CD and has now become a full-fledged operating system. With all this buzz, you might ask yourself about the hype; you can see yourself.
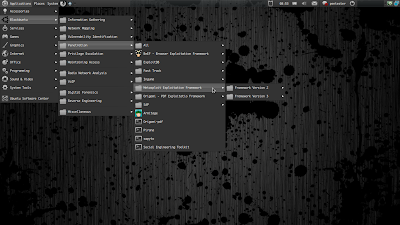
BlackArch

BlackArch Linux is an Arch Linux-based penetration testing distribution for penetration testers and security researchers. The repository contains 2338 tools. You can install tools individually or in groups.
BlackArch Linux is compatible with existing Arch installs. For more information, see the installation instructions.
Blackbuntu
BlackBuntu is a Ubuntu-based distro for Penetration Testing with the Pro’s GNOME Desktop Environment style.
Though this distro has not been updated since Feb 2015 (check on 3rd Sep. 2019).
You can download Blackbuntu here!
Backtrack

BackTrack is a distribution based on the Debian GNU/Linux distribution aimed at digital forensics and penetration testing use. It is named after backtracking, a search algorithm.
The current version is BackTrack 5 R3., now based on Ubuntu 10.04 (Lucid) LTS, next to Debian.
Ipcop
IPCop is a Linux distribution which aims to provide a simple-to-manage firewall appliance based on PC hardware.
IPCop is a stateful firewall built on the Linux netfilter framework.
Though the package was last updated on February 2015, and the current status is Abandoned
You can check more details about the project here:
Network Security Toolkit (NST)

The Network Security Toolkit (NST) is a Linux-based Live CD that provides a set of open-source computer security and networking tools to perform routine security and networking diagnostic and monitoring tasks.
The distribution can be used as a network security analysis, validation and monitoring tool on servers hosting virtual machines.
Pentoo

Pentoo is a Live CD and Live USB designed for penetration testing and security assessment.
Based on Gentoo Linux, Pentoo is provided as 32 and 64-bit LiveCD. It features packet injection patched wifi drivers, GPGPU cracking software, and many tools for penetration testing and security assessment.
The Pentoo kernel includes security and PAX hardening and extra patches – with binaries compiled from a hardened toolchain with the latest nightly versions of some tools available.
Knoppix STD (Security Tools Distribution)

Knoppix STD (Security Tools Distribution) is a Live CD Linux distribution based on Knoppix that focuses on computer security tools.
It included GPL-licensed tools in the following categories: authentication, password cracking, encryption, forensics, firewalls, honeypots, intrusion detection system, network utilities, penetration, packet sniffers, assemblers, vulnerability assessment and wireless networking.
Knoppix STD version 0.1 was published on January 24, 2004, on Knoppix 3.2. Thereafter, the project stagnated, lacking updated drivers and packages. A release date for version 0.2 has not yet been announced. A list of tools is available on the official website.
Helix 3 Enterprise

Helix3 Enterprise is a cyber security solution integrated into your network, giving you visibility across your entire infrastructure, revealing malicious activities such as Internet abuse, data sharing and harassment.
H3E also allows you to quickly isolate and respond to incidents or threats without user detection through a central administration tool. Helix3 Enterprise allows you to quickly Detect, Identify, Analyze, Preserve and Report giving you the evidence to reveal the truth and protect your business.
Damn Vulnerable Linux (DVL)

Damn Vulnerable Linux (DVL) is a Slackware and Slax-based live DVD.
Purposefully stuffed with broken, ill-configured, outdated and exploitable software, the distribution began life as a training system used during the author’s university lectures.
Its primary goal is to design a Linux system that is as vulnerable as possible — to teach and demonstrate a variety of security topics, including reverse code engineering, buffer overflows, shell code development, web exploitation, and SQL injection.
BackBox
BackBox is an Ubuntu-based Linux distribution penetration test and security assessment oriented, providing a network and informatics systems analysis toolkit.
BackBox desktop environment includes a minimal yet complete set of tools required for ethical hacking and security testing.
INSERT Rescue Security Toolkit
INSERT (Inside Security Rescue Toolkit) aims to be a multi-functional, multi-purpose disaster recovery and network analysis system.
It runs from a credit card-sized CD-ROM for convenient transport or download and is a stripped-down version of Knoppix. INSERT provides full read-write support for NTFS partitions using captive-ntfs.
PHLAK (Professional Hacker’s Linux Assault Kit)
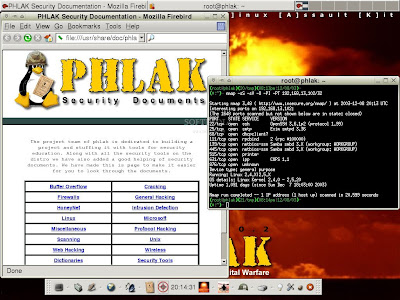
PHLAK (Professional Hacker’s Linux Assault Kit) is a modular security distribution geared to be used as a live CD. PHLAK was created to become the only tool security professionals would need to perform security analysis, penetration testing, forensics, and security auditing.
PHLAK comes with two light GUIs (Fluxbox and XFCE4), packages for printing and publishing, a little multimedia, many security tools, and a file cabinet full of security-related documentation for your reading/educational purposes. This distro is based on Morphix.
Trinity Rescue Kit
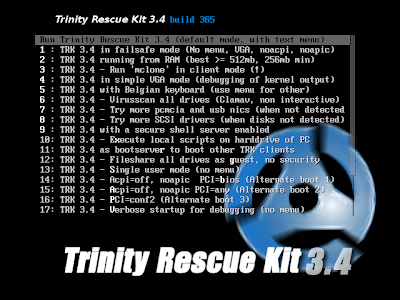
Trinity Rescue Kit (also known as TRK) is a free command-line Live CD Linux distribution created especially for rescuing Windows PCs.
It is aimed specifically at offline operations for Windows and Linux systems, such as rescue, repair, password resets and disk cloning. Its virus scan encompasses five antivirus programs.
Fedora Security Lab

The Fedora Security Lab provides a safe test environment to work on security auditing, forensics, system rescue and teaching security testing methodologies in universities and other organizations.
The development of the Fedora Security Lab (FSL) (formerly known as Fedora Security Spin) provides a media which can be used as a live system.
It provides a promising statement and the fact that it is a fork from Fedora Project and is sponsored by Red Hat.
OPHCrack
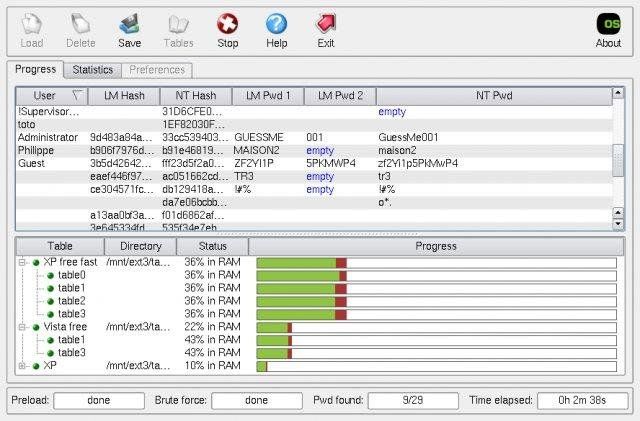
Ophcrack is a free Windows password cracker based on rainbow tables.
It is a very efficient implementation of rainbow tables done by the inventors of the method. It comes with a Graphical User Interface and runs on multiple platforms.
Martiux
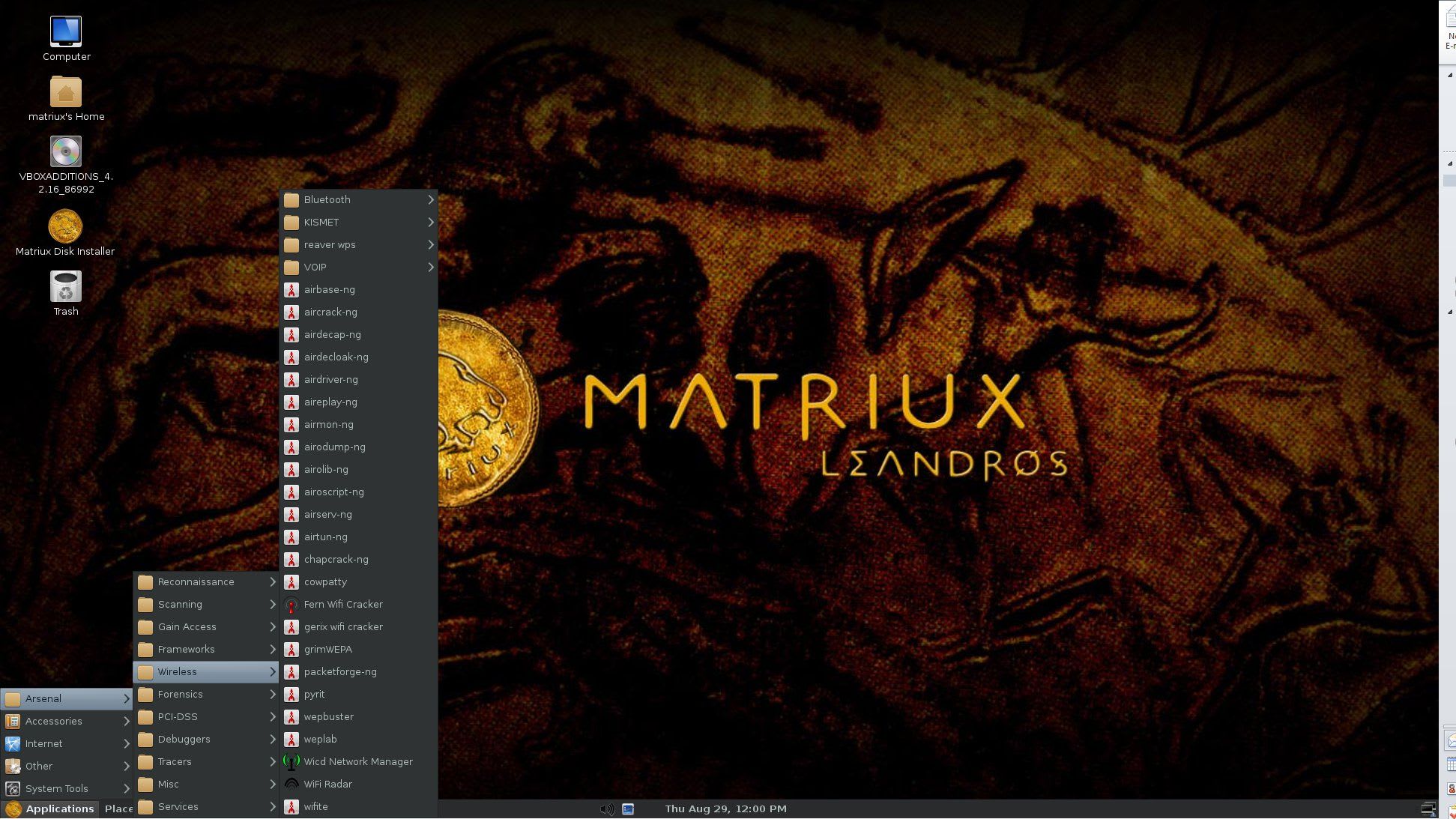
Matriux is a GNU/Linux, Debian-based security distribution designed for penetration testing and cyber forensic investigations. It is a distribution designed for security enthusiasts and professionals and can also be used generally as your default OS.
A more long list can be found at:

Conclusion
Share your views about the above compilation, and if I left your favourite one, please mention them in the comments. or on Twitter at @heypankaj_ and/or @time2hack
If you find this article helpful, please share it with others.
Subscribe to the blog to receive new posts right in your inbox.